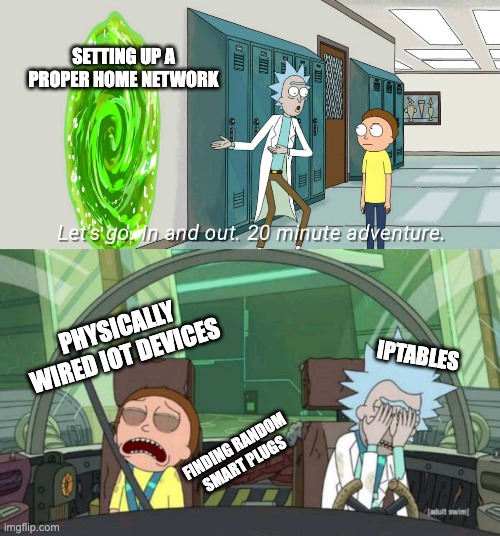
NAT's All, Folks: How I Hardened My Home Network Setup
TOR DOWN FOR WHAT (PART 2): USING TOR
In the first part of this blog entry I discussed the mechanics of the Onion Routing protocol and how Tor provides anonymity. This section is going to focus on the do’s and dont’s of using Tor and how it’s not always an infallible line of defence against prying eyes.
TOR DOWN FOR WHAT (PART 1): HOW TOR WORKS
In this blog post I’m going to dissect Tor (previously an acronym for The Onion Router but now a name in and of itself): how it works and how to use it properly (part two). So this post doesn’t become an entire book, I’m going to assume a basic understanding of cryptography and a somewhat decent command of maths. Nonetheless, I’ll try to explain all concepts clearly and concisely and, where possible, omit needless complexities.
Deobfuscating Javascript Code
In software development, obfuscation is the intentional structuring of code to make it difficult to interpret by humans. Typically, this is done to prevent reverse engineering or to conceal the purpose of the code, which is known as security through obscurity. Many malicious malware binaries obfuscate their code to this end – as do javascript malware exploits, which use javascript and the users browser as their delivery mechanism. Not only does obfuscation render reverse-engineering the malware harder, it also makes it more likely to bypass virus scanners. The virus scanner might be looking for certain signatures (evidence of shellcode payloads, for example) that may go unnoticed if the malware is sufficiently obfuscated.